HIPAA in the Cloud - Part 1
The Health Insurance Portability and Accountability Act of 1996 (HIPAA) guidelines established the Privacy Rule, which granted federal safeguarding to protected health information (PHI). We are now preparing for a new change: the HIPAA HITECH Act Final Rule 2013. The HITECH (which stands for “Health Information Technology for Economic and Clinical Health”) Act’s biggest change relates to entities referred to as “business associates.” One example of a business associate is a billing clearinghouse that handles PHI. The HIPAA HITECH Act Final Rule 2013 (also referred to as the “Omnibus Rule,” among others) went into effect on March 26, 2013. If that date came and went without your knowledge, then it’s time for some catch up. The U.S. Department of Health and Human Services (HHS) gave everyone six months to comply. That date, September 23, 2013, is nearly upon us.
This article is not meant to cover this entire act of Congress - for that, please download the complete, 138-page document that discusses revisions here. This article is meant to introduce the topic and to provide you with a few high impact and actionable steps that will help you establish or maintain your compliance with these regulations. So, let’s get started…
Encryption and PHI
So, what can you do to make sure that you’re maintaining compliance?
- Get familiar with the basics. The Privacy Rule and Security Rule are the main points of focus when thinking about PHI and possible breaches. As we noted in our introductory article, electronic means of storage and transmission have vastly increased the number of possible points of failure and overall complexity of safely maintaining PHI.
- Encrypt electronic PHI (referred to as ePHI). This is the best way to prevent getting fined by the Office of Health and Human Services (HHS). Importantly, providers are not obligated under the Breach Notification Rule to report a breach to patients if the compromised data (PHI) that were compromised were encrypted. This is because it is presumed that the attacker is/will be unable to decrypt the data.
Data encryption is not as imposing as it might sound, and providers who implement this basic security practice are definitely taking a big step in the right direction. So what can you do - today - to make sure any ePHI of which you are the custodian are secure?
Encrypt Hard Drives
- Encrypt your HDD or “User” folder using:
- Windows’ built-in encryption software
- File Vault (for Mac OS X), or
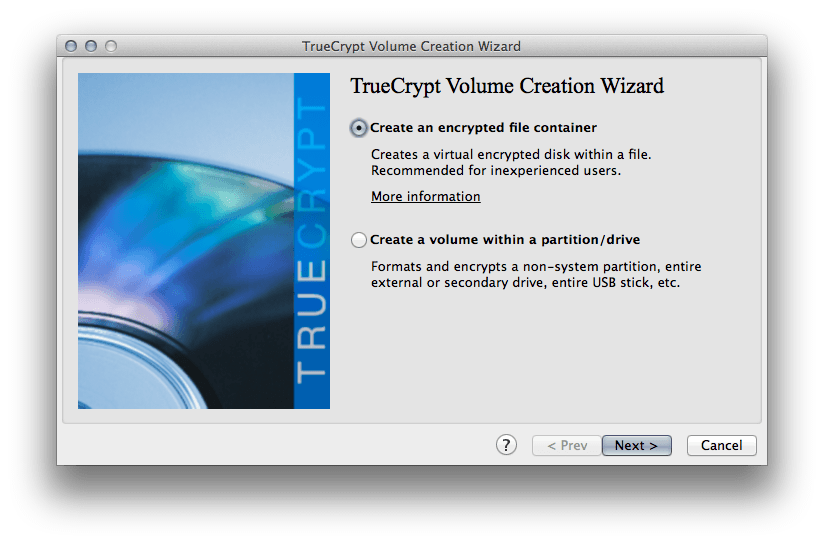
- True Crypt.[1]
Encrypt Email
- All non-encrypted email is sent as plain-text. Information transmitted as plain text is incredibly easy to intercept, and there is absolutely no security to prevent anyone from reading it exactly as it was written. [2]
- HIPAA HITECH rules do not explicitly state that email must be encrypted; however, it is pretty much exactly what needs to be done.
- How to Encrypt your email:[3]
De-Identify PHI
- De-identifying PHI can also be very, very effective, especially since HHS recommends it. In fact, HHS have published a set of guidelines to help with the process.
The information in this article should get you moving toward HITECH compliance. Please don’t hesitate to contact us with any other thoughts, ideas or questions about this important, complex topic! We will have more to come as September 23rd approaches, so remember to check back or subscribe to Articles using our RSS Atom feed!
-
TrueCrypt is amazing. In addition to creating simple encrypted folders, it can even create an entire, hidden operating system. Downloads are available for many operating systems, which is also nice. ↩
-
Think about this in other contexts, too, like sending your significant other your bank account or other sensitive data. ↩
-
These are all open-source software packages, and are free to download. ↩


